April 8, 2024: This brief article highlights some of the compelling points from the statement of facts in the
Who Do We Turn to When the US Government, CDC, NIH, and FDA ‘Get It Wrong’?
Commissioner Hall was and is correct in stating that our government made mistakes during COVID. The US government and healthcare agencies, including the FDA, CDC, NIH, American Medical Association, American Academy of Pediatrics and many others made egregious mistakes resulting in the injury, harm, and even death of innocent children and adults across America.
I opened my presentation in agreement with Commissioner Hall by posing the question; “Who Do Collier County Residents Turn to When the Federal Government and Healthcare Agencies Get it Wrong?”
You can view my 8-minute presentation here.
Transcript of Karen Kingston March 28, 2023 Presentation
Thank you commissioners. My name is Karen Kingston. I’m a Med-legal analyst and biotech analyst. I have 25 years of experience. My work has been recently used in a number of lawsuits across America to prosecute Pfizer and it’s also being used in global criminal investigations for Pfizer as well.
First, I’d like to thank you for giving me opportunity to speak with you. My family is here. They’re not here right now, but they are here with me in Naples and we’re going to be moving here this summer. I am very much invested in this community.
You have a community of soldiers.
Something that Colin Powell said is that leadership is about your soldiers being able to bring problems to you. Your job is to solve problems and when your soldiers stop coming to you, then you’re no longer a leader.
So, as Commissioner LoCastro had said, you have a community of soldiers here and they look to you as their leaders and they trust you and they respect you and they come to you and they’re comfortable coming to you to say. “These are our issues. These are our problems, and we would like your help. We’d like your support in overcoming these issues and to protect us and to protect our children.”
What happens when the federal government and healthcare agencies get it ethically wrong?
Let’s say they get the facts wrong, and they get the Constitution wrong. What do we do? Because as Commissioner Hall had said, you’re here to protect our constitutional rights, and to make sure that they’re not violated. But when constitutional rights are violated and it’s intentional, under 18 USC 241, that’s conspiracy to violate rights, and 18 USC 242, it’s pretending under the color of law that you have the right to take away people’s constitutional rights, when you do not. And when this happens, it should result in criminal investigations, especially if the civil rights violations result in the disease, disabilities, and deaths of innocent civilians.
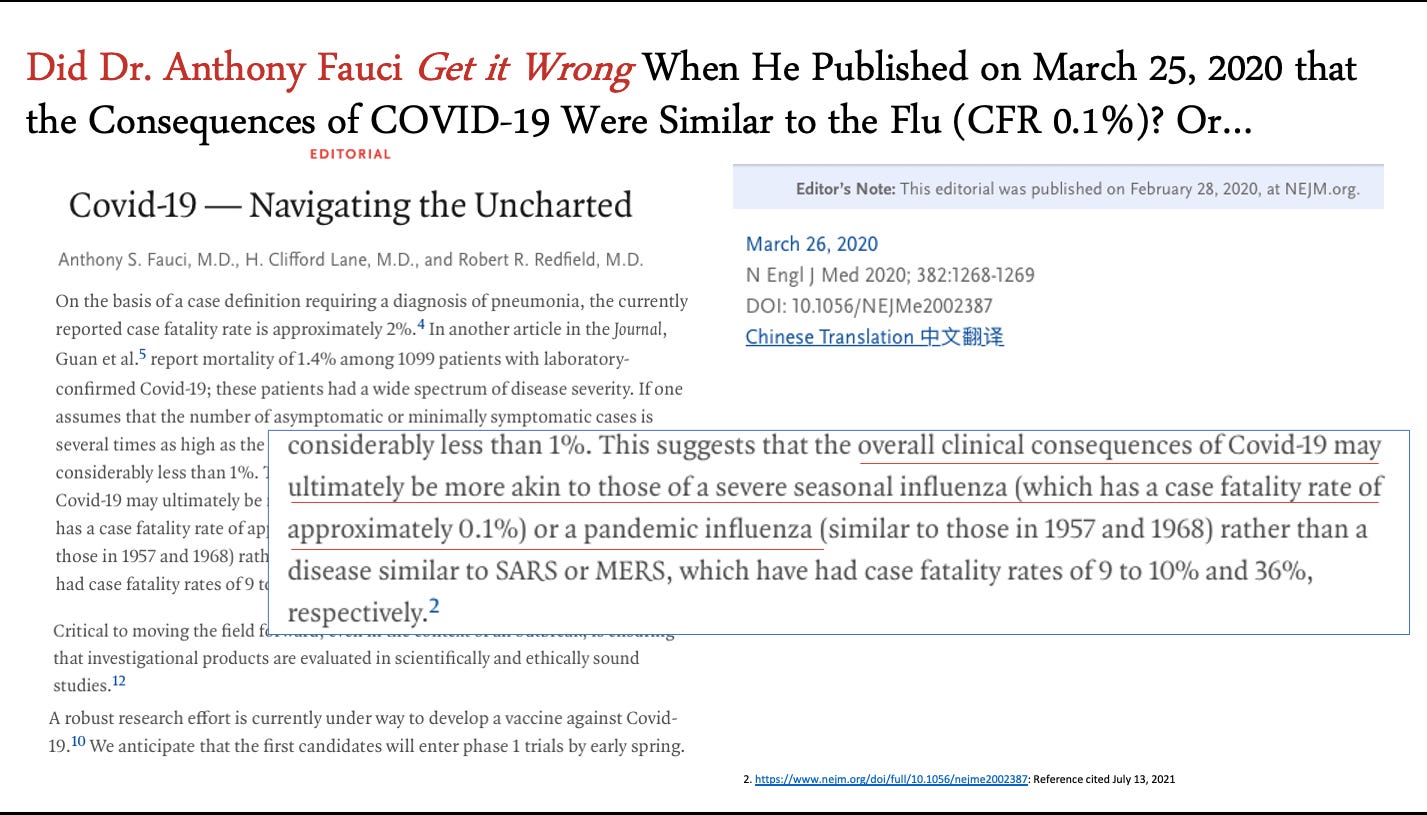
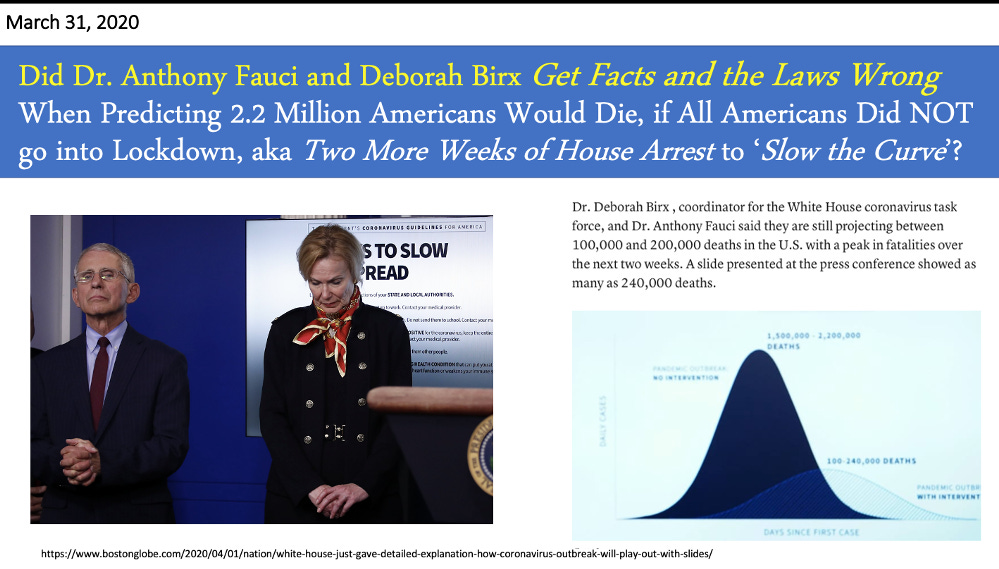
So, did Fauci get it right? Or get it wrong when he said we need to lockdown the country?
On March 26, 2020, Fauci had said that the COVID-19 virus has a 0.1% case fatality rate similar to the flu.
Five days later, Fauci and Birx get on national stage next to President Trump, and they said, “2.2 million people are going to die if we don’t lockdown our nation and make everyone go on house arrest.”
The lockdowns were a violation of civil rights.
Did they get that wrong? They certainly got it ethically wrong. And it was a violation of civil rights to make people go under house arrest.
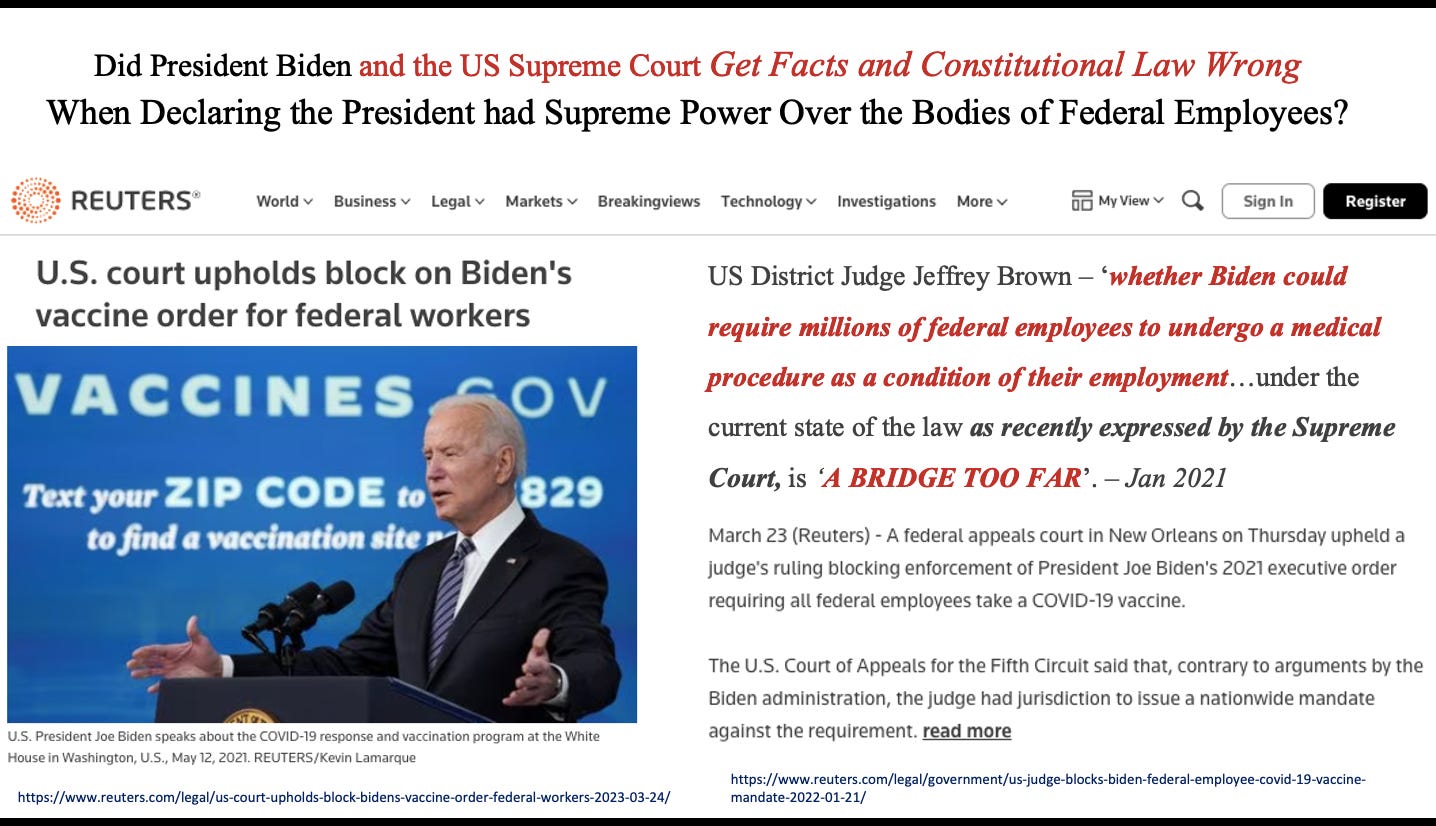
The vaccine mandates were a violation of civil rights.
Did President Biden get it wrong when he passed a mandate through OSHA for all employers to vaccinate their employees? Yes, he did and his OSHA mandate was overthrown in 2021.
Then Biden made a mandate for just the federal workers throughout 2022. Five (5) Federal court judges said Biden had overstepped his boundaries. And just on March 23rd, a Federal judge in New Orleans said Biden definitely overstepped his boundaries and that the Federal judge in Texas got it right. The Federal judge stated, “If Biden can require millions of federal employees to undergo a medical procedure as a condition of their employment, that’s a bridge too far.”
So both President Biden and the US Supreme Court got it wrong. Under 18 USC 241, that is conspiring to violate people’s civil rights. If it results in disease, disabilities, or death, it can be punished by life imprisonment.
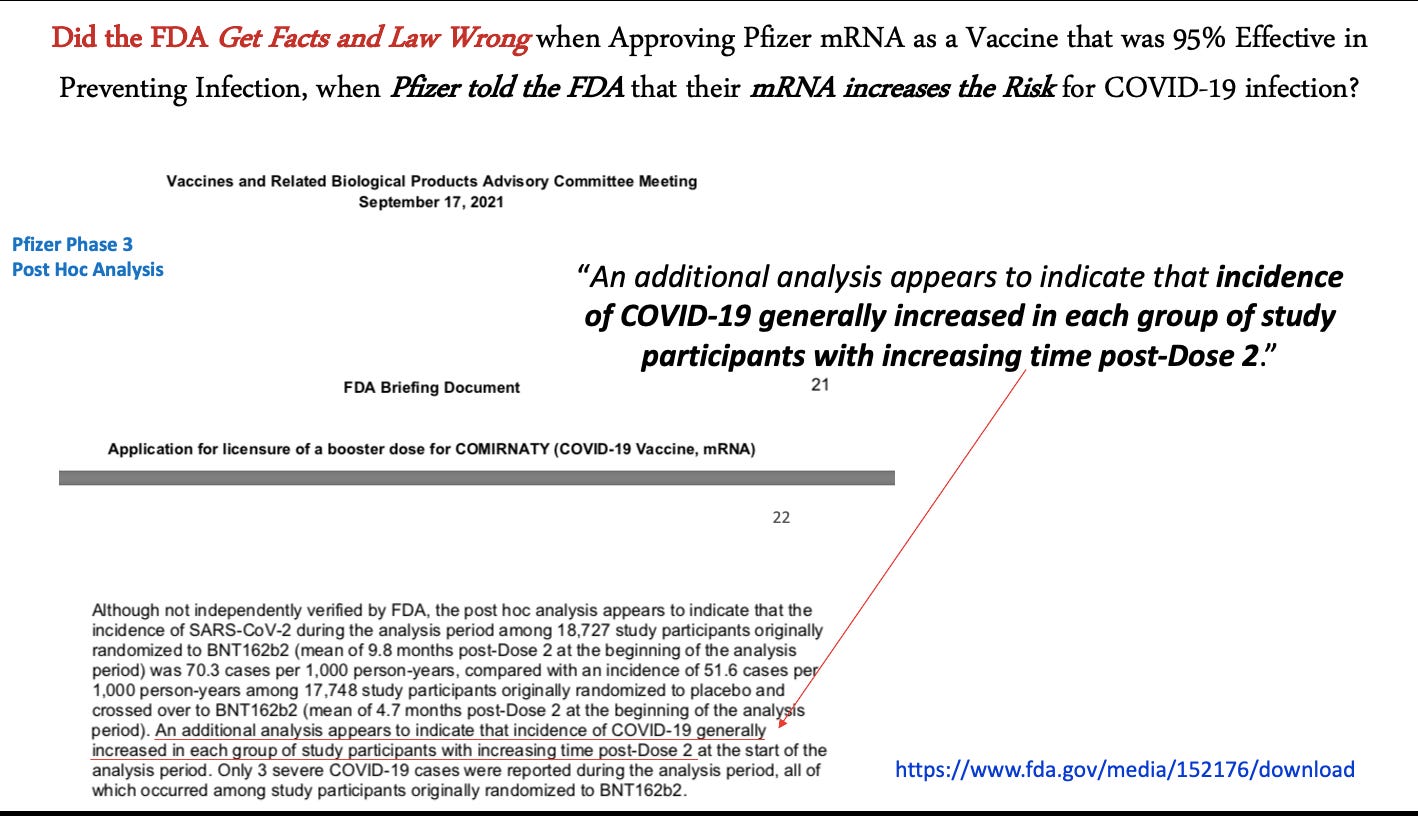
The FDA and Pfizer knowingly and fraudulently promoted harmful biological agents as safe and effective vaccines. This is criminal.
Did Pfizer get it wrong and the FDA get it wrong when they said that this product, that their ‘vaccine’ prevents COVID-19 infection?
When considering that on September 17, 2021, Pfizer told the FDA that actually, it turns out once you get two more shots, you’re more likely to get infected with the disease (over time).
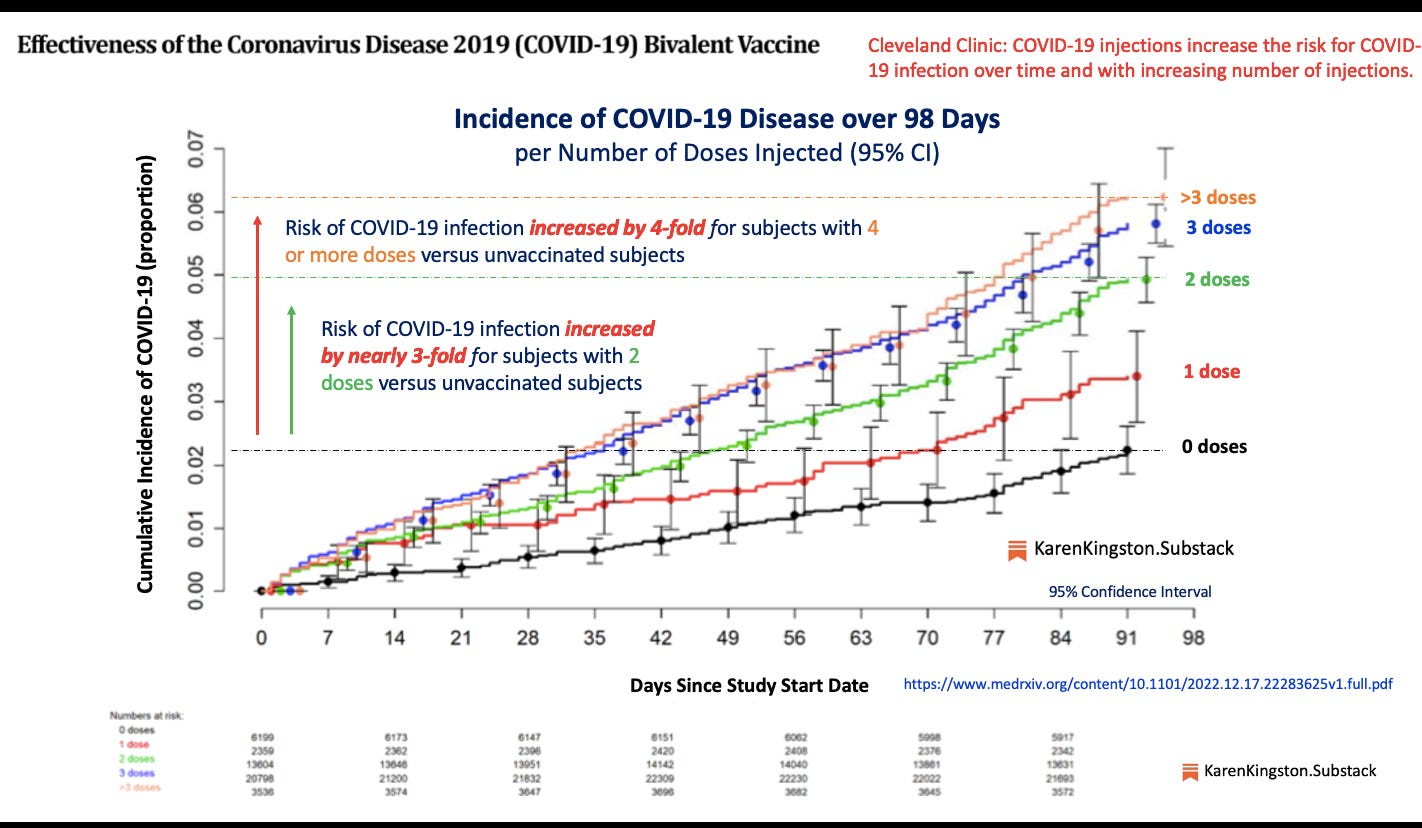
(The fact that the Pfizer and Moderna mRNA injections cause COVID-19 was confirmed by a study of 51,000 employees from the Cleveland Clinic).
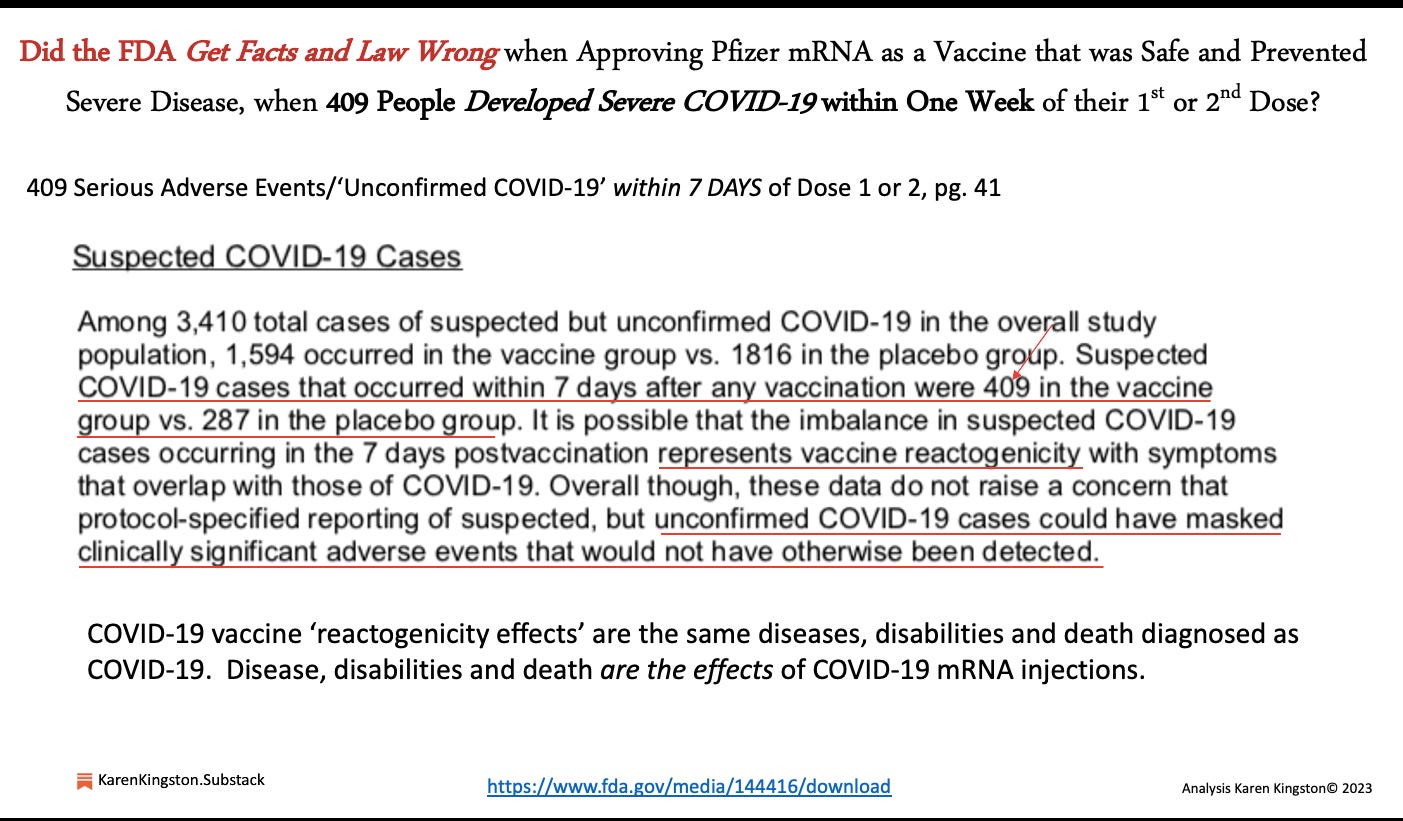
Also, they (the FDA and Pfizer) said it would prevent hospitalizations and it was safe, even though on November 20th, Pfizer told the FDA, “actually after study subjects got our shots, 409 people came down with severe COVID, meaning they were likely either hospitalized or they could have died.” And that will happen within one week of the shot. The shots don’t prevent hospitalization, they cause hospitalizations.
The FDA and Pfizer knowingly conducted criminal human experiments.
Did they get it wrong?
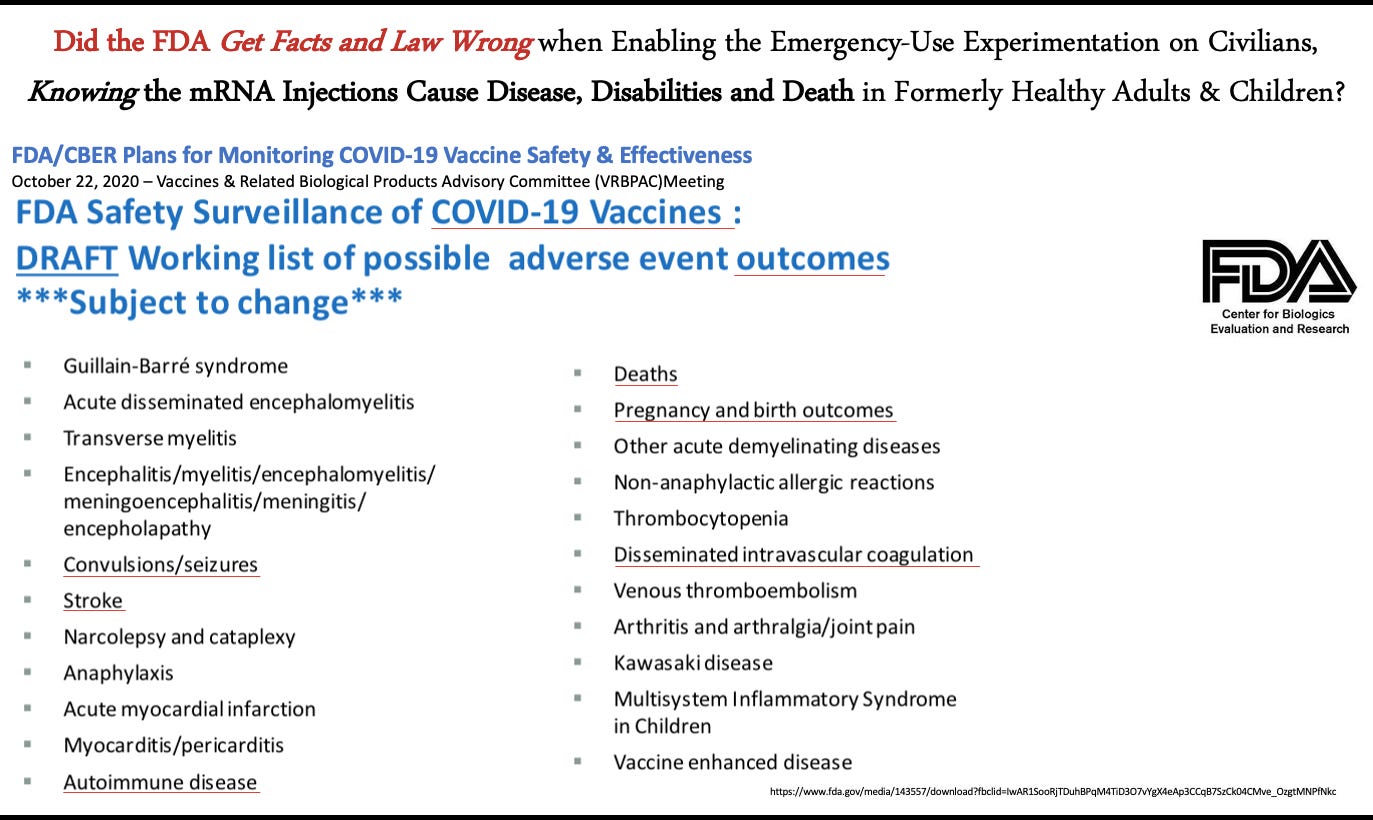
Did they get it wrong when on October 22, 2020, the FDA met with all pharmaceutical companies, and they said, “we know these mRNA injections are going to cause disease, disabilities, death, heart attacks, blood clotting, pregnancy outcomes, and birth defects.”
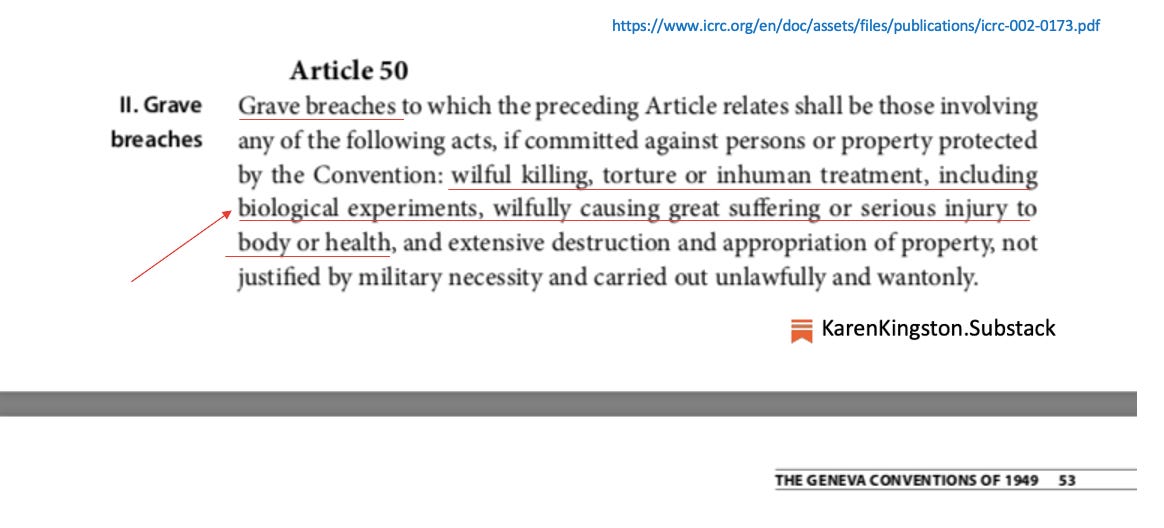
This is is a violation of the Nuremberg Code and of the Geneva Code, Article 50.
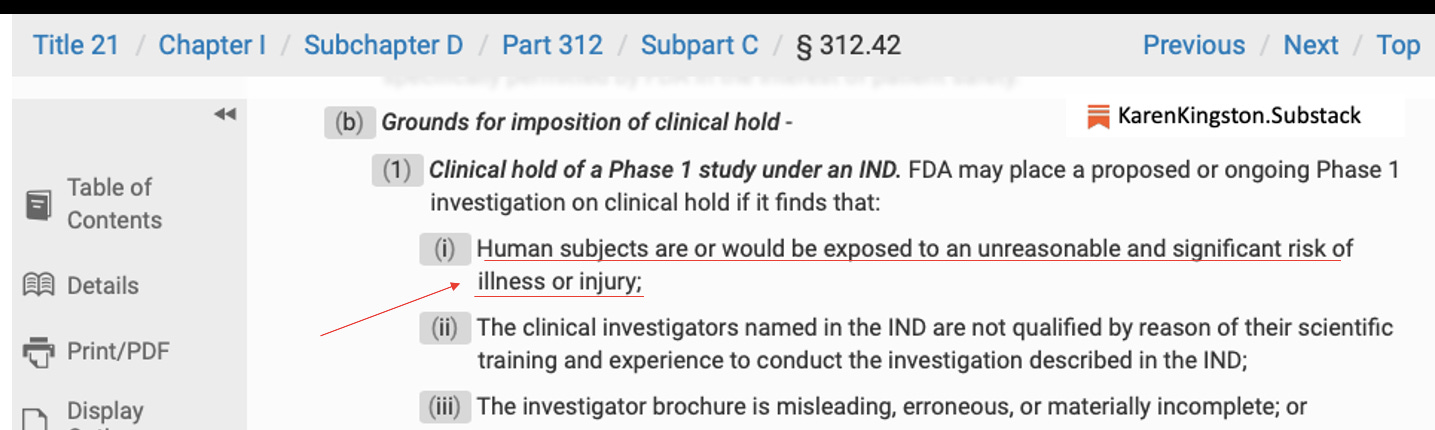
(Under 21 USC), you’re not allowed to move forward with clinical trials in humans when you know that the experiment is going to put children, adults, and otherwise healthy individuals at unnecessary risk.
Did they get that wrong?
Did they get informed consent wrong?
Did they get it wrong when on December 16, 2016, Obama and Congress signed into law, the CURES Act and under Section 3024 it states that “under the experimental use of emergency-use authorized products informed consent is not necessary, if it is not in the best interest to such human beings.”
As Scott Kiley said, this is a violation of the Nuremberg Code. It’s also in violation of Article 50 of the Geneva code. (The use of Pfizer’s mRNA injections on adults and children is criminal human experimentation, aka biowarfare.)
Did the FDA get it wrong when they said we should experiment on children? And on babies, six months to four years of age?
This was submitted in June 15, 2022.
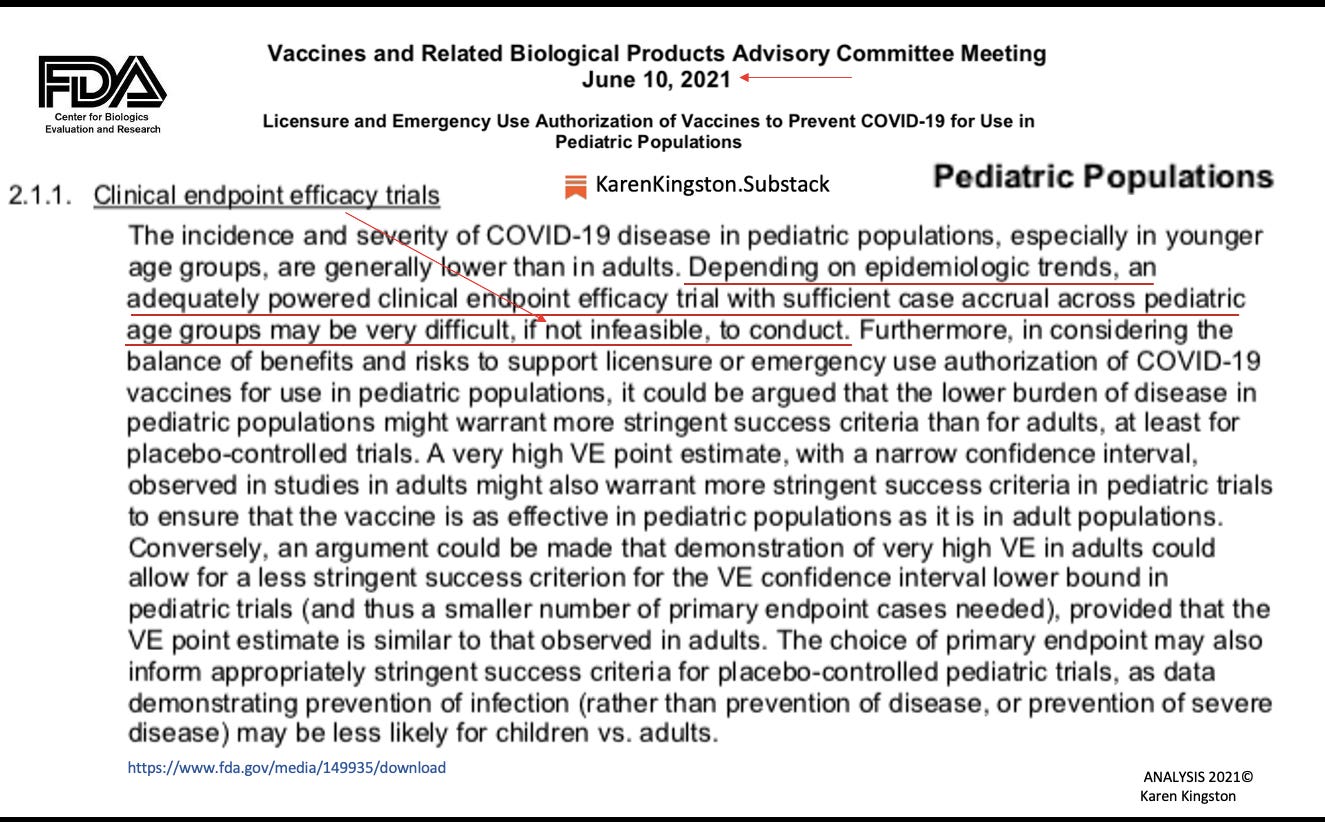
Now, one year and five days earlier, the FDA met with the pharmaceutical companies, and they said, “it’s statistically impossible for us to develop a vaccine that’s going to be more effective against the COVID-19 virus than a child’s own immune system.”
So they should have never even move forward with experimenting on these babies; again ages six-months to 4-year-olds.
This study is of four-thousand and five-hundred (4,500), 6-month-old babies to 4-year-old toddlers. Only 25% of these babies (and toddlers) made it to the end of the study.
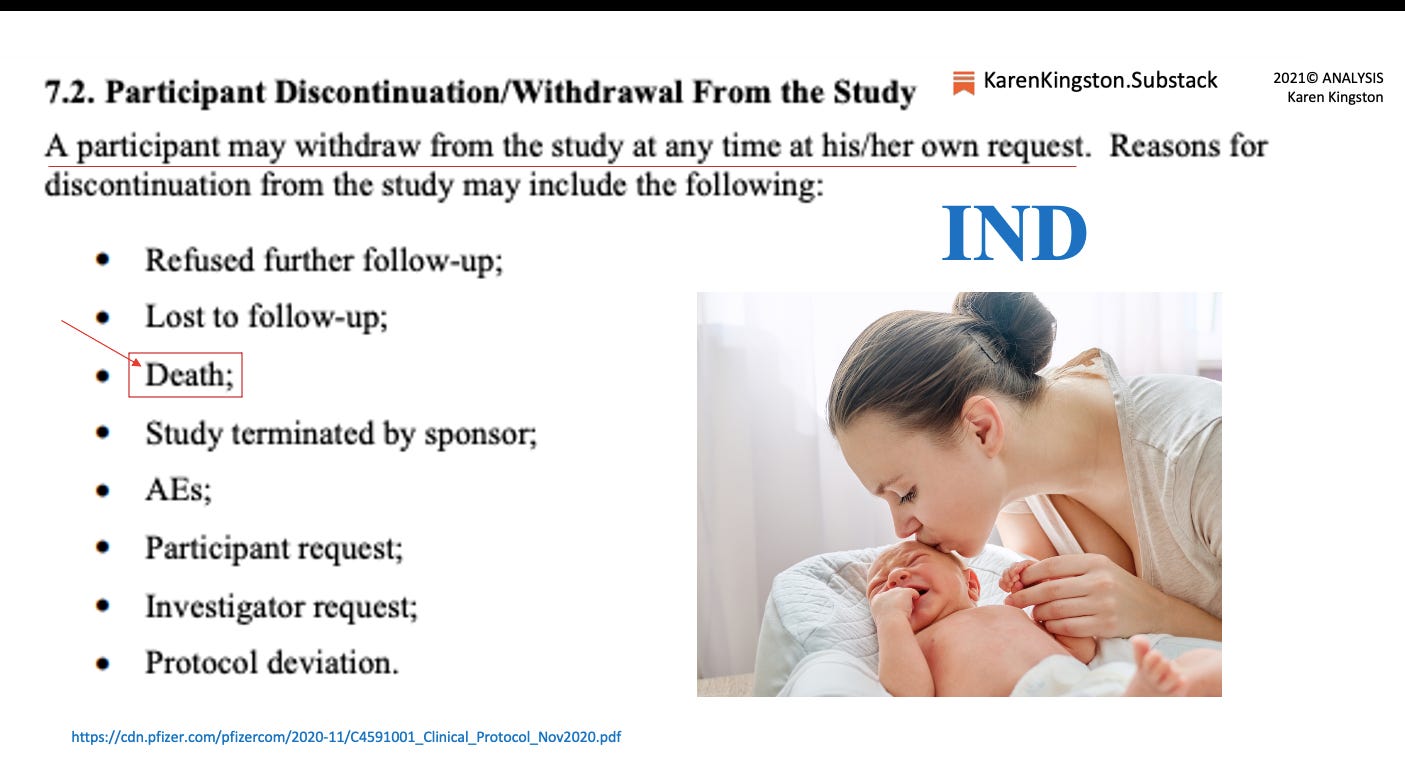
The other 75% withdrew. Reasons for withdrawal were; serious adverse events, the parent decided to pull them out of the study, and death was a reason for withdrawal. I’ve never heard of anyone calling in to request to be withdrawn from a clinical trial because they were dead.
“We don’t know what happened to 75% of those babies.” – Karen Kingston
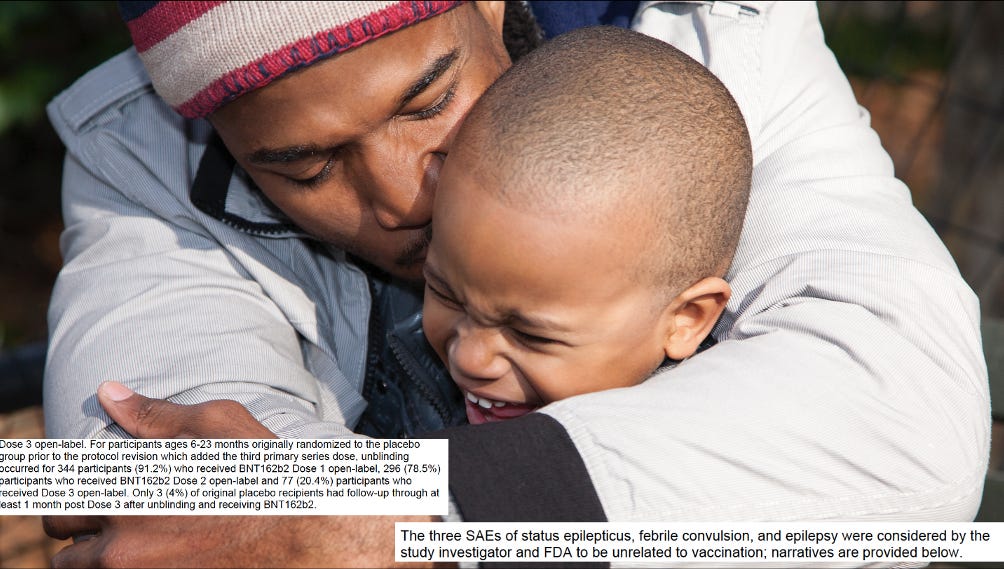
In the toddler group, a number of the babies had something called status epilepticus. There are dozens of them. They had seizures, multiple seizures, multiple times a day. And Pfizer said, “well that is not from our product.”
There’s one I want to read to there was a 4-year-old with an alleged family history of seizures, actually they did not have it. (The babies and toddlers had to be perfectly healthy prior to enrolling in the trial). They had seizures every day and high fever and the study investigator stated that these clinical outcomes were unrelated to the BNT162b2 vaccine, but they said it’s possibly related to the flu vaccine.
This data is so manipulated, it’s ridiculous. They would never allow a 4-year-old child in a vaccine study to then get a flu vaccine. Again, the reasons for withdrawal are refused further follow-up, lost to follow-up, and death. I’ve never heard anyone calling in to say, “I’d like to withdraw from the study because I died.”
Only 3 out of 344 Babies Made it their 3-month Follow-Up Visit
One other point I’d like to make is that there were 344 babies who were injected with… well…they were supposed to get injected with three shots of Pfizer shot. Only three babies made it to the end of the study. Only three babies (of the 344) made it one week post the third dose.
“We don’t know what happened to 341 babies.” (They could have been permanently disabled or died.)
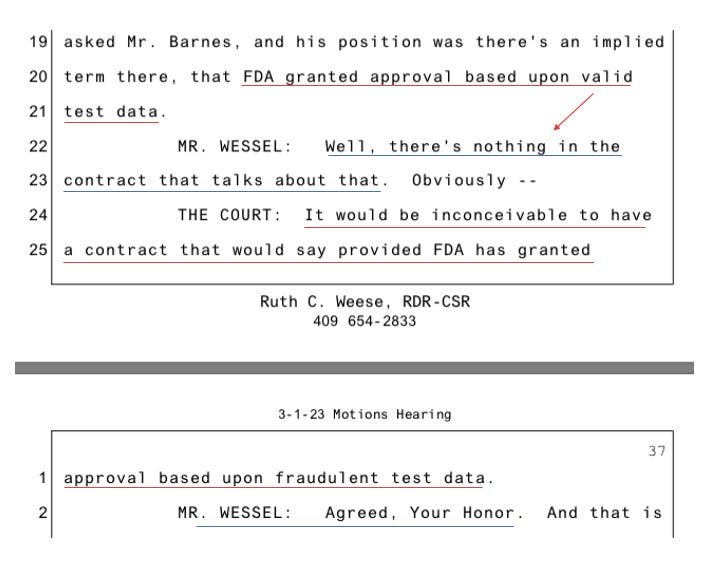
Did Pfizer and the FDA ‘Get it Wrong’ When Admitting that ‘If’ They Conspired to Commit Crime, There is Nothing Anyone Can Do About It?
Last thing, I’d like to say is that in the Brook Jackson case, which is a $3 trillion case vs Pfizer, Pfizer basically says, “we committed fraud with the FDA… or if we had, it’s okay because the FDA says that’s fine.”
And the judge said to Pfizer, “So what you’re saying is if the FDA gets it wrong…” And Pfizer said, “Yes, Your Honor.” And the judge goes on, “They just get it wrong and we live with it. There was no oversight by a court. That’s it. That’s correct?”
And Pfizer’s attorney said, “Yes, Your Honor.”
So, Pfizer and our federal government is saying no matter what they do, no matter how many rights they violate, no matter how many people and children they cause disability, disease, and death upon, there is nothing anyone can do to stop them.
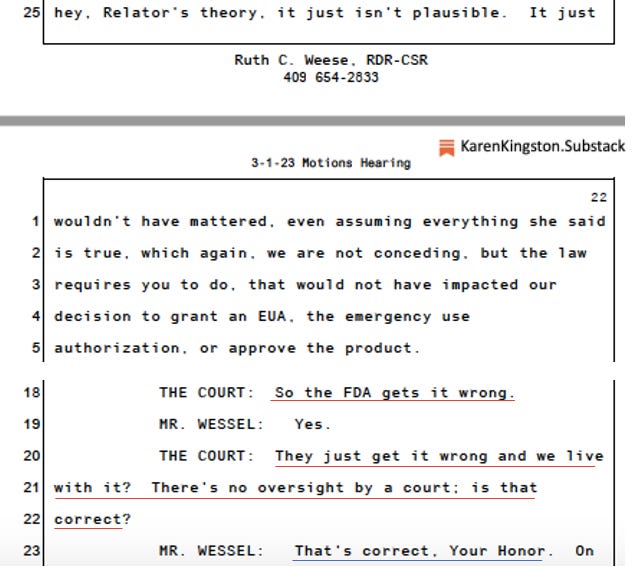
Who do the residents of Collier County turn to protect women and children?
So, who do the residents of Collier County turn to, to protect the children, the women and all residents when the FDA and the federal government and state governments get it wrong? They turn to you.
And I ask that you get on the right side of history or put Collier County on the right side of history, as we move forward in this war to protect Americans and to protect the Constitution. I ask that you pass the resolution as well as to pass the ability to evaluate the ordinance to be forward for a vote. Thank you.
Commissioner Hall Got It Right.
“The resolution is a resolve, is a posture that I would like to see us adopt for anything that comes in the future, if we see something coming in the future that violates our Constitutional rights that are given to us by God Almighty. The Constitution doesn’t give us our rights. The Florida State Constitution doesn’t give us our rights.
Our rights are inalienable by God Himself. We live in America, and America was founded on Godly principles. I’m not ashamed to say it and I’ll say it boldly and that’s the stance that I’m taking.” – Commissioner Chris Hall, March 28, 2023
The Kingston Report. TRUTH WINS.
Exodus 18: 19-21
“Listen now to me and I will give you some advice, and may God be with you.You must be the people’s representative before God and bring their disputes to him. Teach them his decrees and instructions, and show them the way they are to live and how they are to behave. But select capable men from all the people—men who fear God, trustworthy men who hate dishonest gain—and appoint them as officials over thousands, hundreds, fifties and tens.”
– Jethro, Moses’ father-in-law
Expertise and Intelligence is Required to Win an Intelligence War
Ways to Support My Work
Mail: Karen Kingston/miFight Inc., 960 Postal Way #307, Vista, CA 92085
Consider becoming a free or paid subscriber.
email: [email protected]
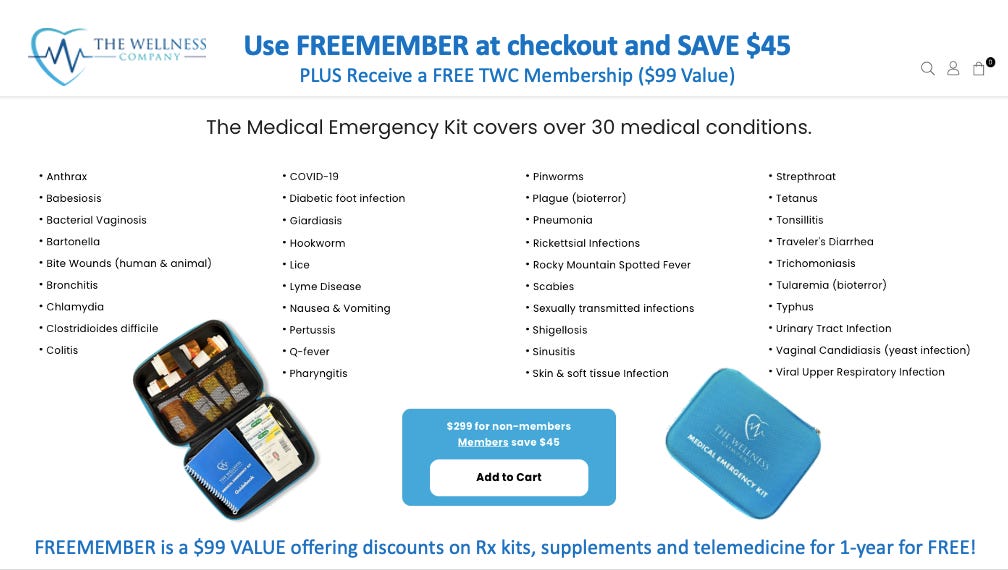
Get a FREE $99 Wellness Company Membership
You can keep a full armamentarium of prescriptions on-hand for bacterial, viral, or parasite infections through The Wellness Company. Use the code FREEMEMBER at checkout and SAVE $45.